Atm Password Hacker Software Download
Get ready for a facepalm: 90% of credit card readers currently use the same password.
Dec 31, 2018 Wifi Password Hacking Software v3.47 free download is the best software because quite quickly you could just click on the button & hack any WIFI without hesitation. It is now possible to approach any router without getting permission from a person or authority. Wifi-Password Hacker Free Download available. WIFI Hacker 2019 has many advantages. Jan 20, 2014. Remember for using credit card on internet u don't need PIN ( 4 words password which u enter in ATM Machine ), but for cashout u need. After you create your scam site, just find some email harvestor or spider from internet (download good one at Bulk Email Software Superstore - Email Marketing.
The passcode, set by default on credit card machines since 1990, is easily found with a quick Google searach and has been exposed for so long there's no sense in trying to hide it. It's either 166816 or Z66816, depending on the machine.
With that, an attacker can gain complete control of a store's credit card readers, potentially allowing them to hack into the machines and steal customers' payment data (think the Target(TGT) and Home Depot(HD)hacks all over again). No wonder big retailers keep losing your credit card data to hackers. Security is a joke.
Download Password Hacker Free
This latest discovery comes from researchers at Trustwave, a cybersecurity firm.
Administrative access can be used to infect machines with malware that steals credit card data, explained Trustwave executive Charles Henderson. He detailed his findings at last week's RSA cybersecurity conference in San Francisco at a presentation called 'That Point of Sale is a PoS.' God of war 3 game free download for laptop.
The problem stems from a game of hot potato. Device makers sell machines to special distributors. These vendors sell them to retailers. But no one thinks it's their job to update the master code, Henderson told CNNMoney.
'No one is changing the password when they set this up for the first time; everybody thinks the security of their point-of-sale is someone else's responsibility,' Henderson said. 'We're making it pretty easy for criminals.'
Trustwave examined the credit card terminals at more than 120 retailers nationwide. That includes major clothing and electronics stores, as well as local retail chains. No specific retailers were named.
The vast majority of machines were made by Verifone(PAY). But the same issue is present for all major terminal makers, Trustwave said.
A spokesman for Verifone said that a password alone isn't enough to infect machines with malware. The company said, until now, it 'has not witnessed any attacks on the security of its terminals based on default passwords.'
Just in case, though, Verifone said retailers are 'strongly advised to change the default password.' And nowadays, new Verifone devices come with a password that expires.
In any case, the fault lies with retailers and their special vendors. It's like home Wi-Fi. If you buy a home Wi-Fi router, it's up to you to change the default passcode. Retailers should be securing their own machines. And machine resellers should be helping them do it.
Trustwave, which helps protect retailers from hackers, said that keeping credit card machines safe is low on a store's list of priorities.
'Companies spend more money choosing the color of the point-of-sale than securing it,' Henderson said.
This problem reinforces the conclusion made in a recent Verizon cybersecurity report: that retailers get hacked because they're lazy.
The default password thing is a serious issue. Retail computer networks get exposed to computer viruses all the time. Consider one case Henderson investigated recently. A nasty keystroke-logging spy software ended up on the computer a store uses to process credit card transactions. It turns out employees had rigged it to play a pirated version of Guitar Hero, and accidentally downloaded the malware.
'It shows you the level of access that a lot of people have to the point-of-sale environment,' he said. 'Frankly, it's not as locked down as it should be.'
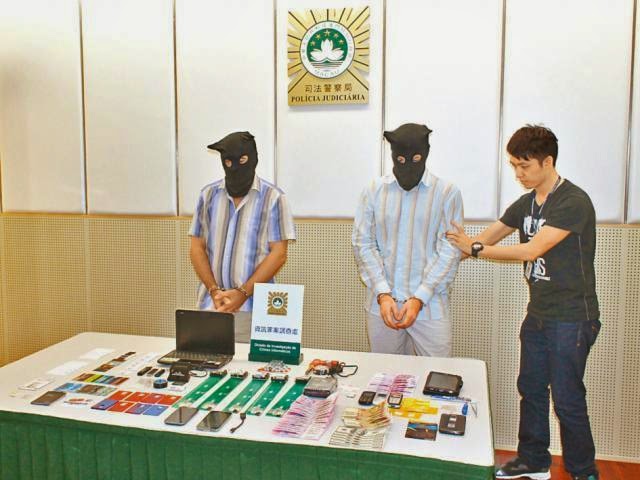
We have already told you about a number of hacker groups jackpotting money from ATMs. Now you can see it with your own eyes! Our experts shot four videos of ATM hack demos. Disclaimer: No bank was harmed in the process, and we do not recommend you try any of these methods.
Method 1: Fake processing center
This method requires an attacker to access a cable connecting the machine to the network. The hacker disconnects the ATM from the bank’s network and then connects it to an appliance that acts as a fake processing center.
The box is used to control the cash trays and send commands to the ATM, requesting money from the chosen tray. It’s as simple as that: The attacker can now use any card or input any PIN code, and the rogue transactions will look legitimate.
Method 2: A remote attack on several ATMs
This method involves an insider working in the target bank. The criminal purchases a key from the insider that opens the ATM chassis. The key does not give an attacker access to the cash trays, but it exposes the network cable. The hacker disconnects the ATM from the bank’s network and plugs in a special appliance that sends all of the data to their own server.
Networks connecting ATMs are often not segmented (separated for security), and ATMs themselves can be configured incorrectly. In that case, with such a device a hacker could compromise several ATMs at once, even if the malicious device is connected to only one of them.
Password Hacker Software
The rest of the attack is carried out just as described in Method 1: A fake processing center is installed on the server, and the attacker gains full control over the ATMs. Using any card, a criminal can withdraw all of the cash from an ATM, regardless of the model. The only thing the ATMs need to have in common for this method to work is the protocol they use to connect to the processing center.
Method 3: The black box attack
As previously described, the attacker obtains the key to the ATM chassis and accesses it, but this time puts the machine into maintenance mode. Then the hacker plugs a so-called black box into the exposed USB port. A black box in this case is a device that allows an attacker to control the ATM’s cash trays.
While the attacker tampers with the ATM, its screen displays a service message like “Maintenance in progress” or “Out of service,” although in reality the ATM can still draw cash. Moreover, the black box can be controlled wirelessly via a smartphone. The hacker just taps a button on the screen to get the cash and then disposes of the black box to hide the evidence that the machine was compromised.
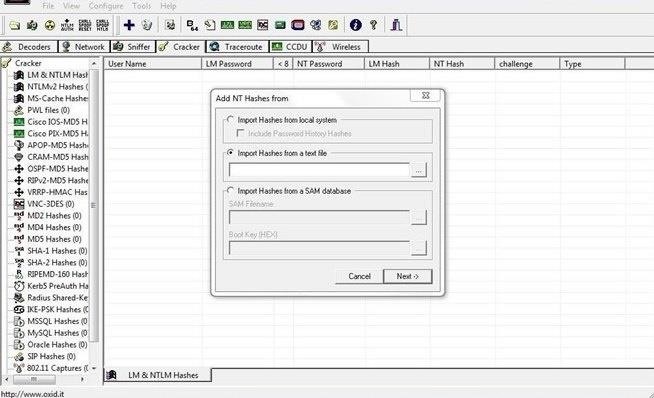
Method 4: Malware attack
Atm Hacking Software
There are two ways to infect a target ATM with malware: by inserting a malware-laced USB drive into the port (requiring the key to the ATM chassis) or by infecting the machine remotely, having first compromised the bank’s network.
If the target ATM is not protected against malware or does not employ whitelisting, a hacker can run malware to send commands to the ATM and make it dispense cash, repeating the attack until the cash trays are empty.
Of course, not all ATMs are hackable. The attacks described above are feasible only if something is misconfigured. It could be that the bank’s network is not segmented, or authentication is not required when the ATM’s software exchanges data with the hardware, or there is no whitelist for apps, or the network cable is easily accessible.
Unfortunately, such problems are rather common. For example, they allowed attackers infect a number of ATMs with the Tyupkin Trojan. Experts at Kaspersky Lab are always ready to help banks fix these issues: We offer consulting services and can audit a bank’s infrastructure and test it for resilience to attacks.